Troy Hunt makes open-source “Have I been Pwned” – site that tells you if your password has been hacked
Nowadays, we nearly accept it as a given that extremely poor security will unavoidably uncover a portion of your usernames and passwords to the world — that is the reason 2FA is so significant, and why you may need a secret phrase test device like the ones currently incorporated with each cutting edge program (well, Safari is coming soon) so you can rapidly supplant the ones that were taken.
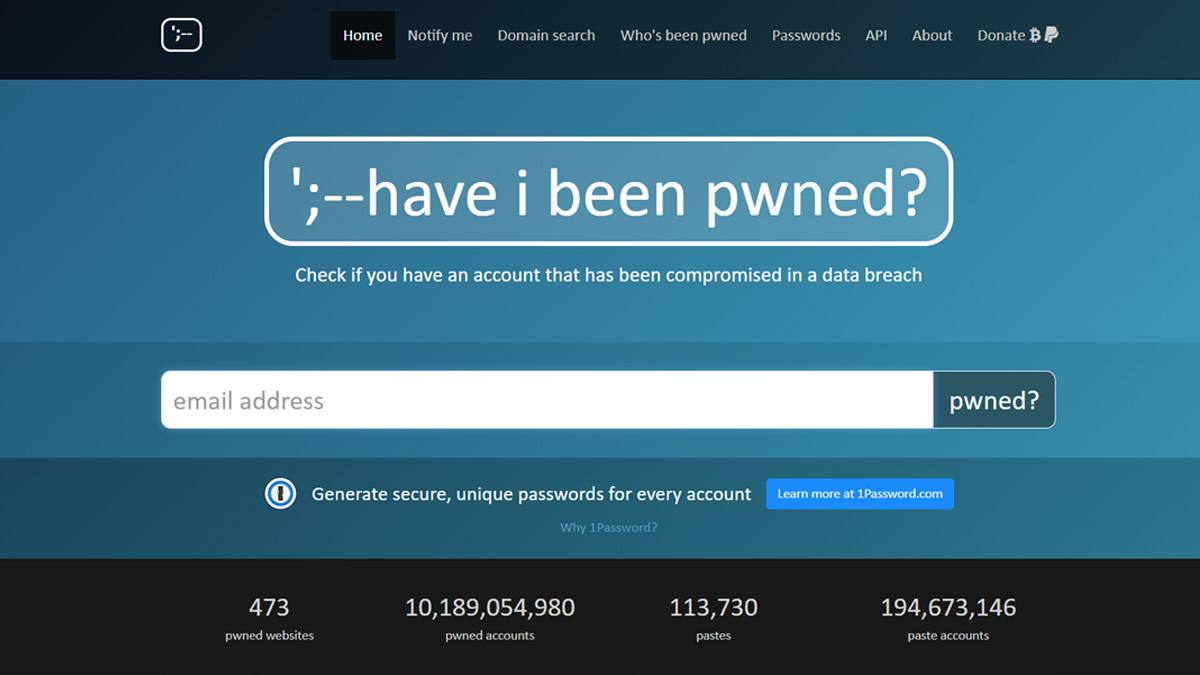
However, almost those secret phrase test instruments owe something to Troy Hunt’s Have I Been Pwned, which was somewhat of an original thought when it previously propelled 7 years back — and Hunt is presently publicly releasing his site codebase so the thought can spread considerably further.
While not all secret word exam devices really utilize Hunt’s database (a simply declared LastPass include approaches one facilitated by Enzoic rather), a considerable lot of them are clearly founded on the equivalent “k-Anonymity” API that Cloudflare building chief Junade Ali initially intended to help Have I Been Pwned’s apparatus.
The significant thought here is that you need to have the option to tell clients that their secret phrase has been penetrated without giving a chance to troublemakers to make sense of which passwords those are and aggravate the break even; k-Anonymity utilizes math to make it harder for programmers.
In any case, Hunt said a year ago that he wouldn’t like to proceed with this without anyone else, he needs the plan to grow, and after a bombed endeavor to get another organization to procure HIBP without settling on a rundown of goals, he’s currently going to attempt to open everything up for the network to contribute.
Note, however, that it’s not exactly occurring yet. Chase composes that he doesn’t have a course of events for opening it up, mostly in light of the fact that it’s in an untidy state, and incompletely on the grounds that he needs to ensure he can keep the databases of penetrated passwords themselves from falling into an inappropriate hands. In light of present conditions, I envision it’ll occur before we figure out how to dispose of passwords out and out, yet it may be far away.


