A virus in the Chrome browser called ChromeLoader is circulating through pirated games and QR codes

As per the news, it claims that the ChromeLoader virus is being utilized in a new malvertising effort to hijack browsers and steal data. According to Red Canary’s Aedan Russell, a sudden, unexpected rise in browser hijacking campaigns leveraging ChromeLoader malware has been observed recently.
The attackers’ goal, according to Russell, is to hijack browsers using the “pervasive and persistent” ChromeLoader malware, which can change browser settings and send victims to ad sites. The attackers are part of a larger network of marketing affiliates who route the user to advertising sites, hence the malvertising effort is financially driven.
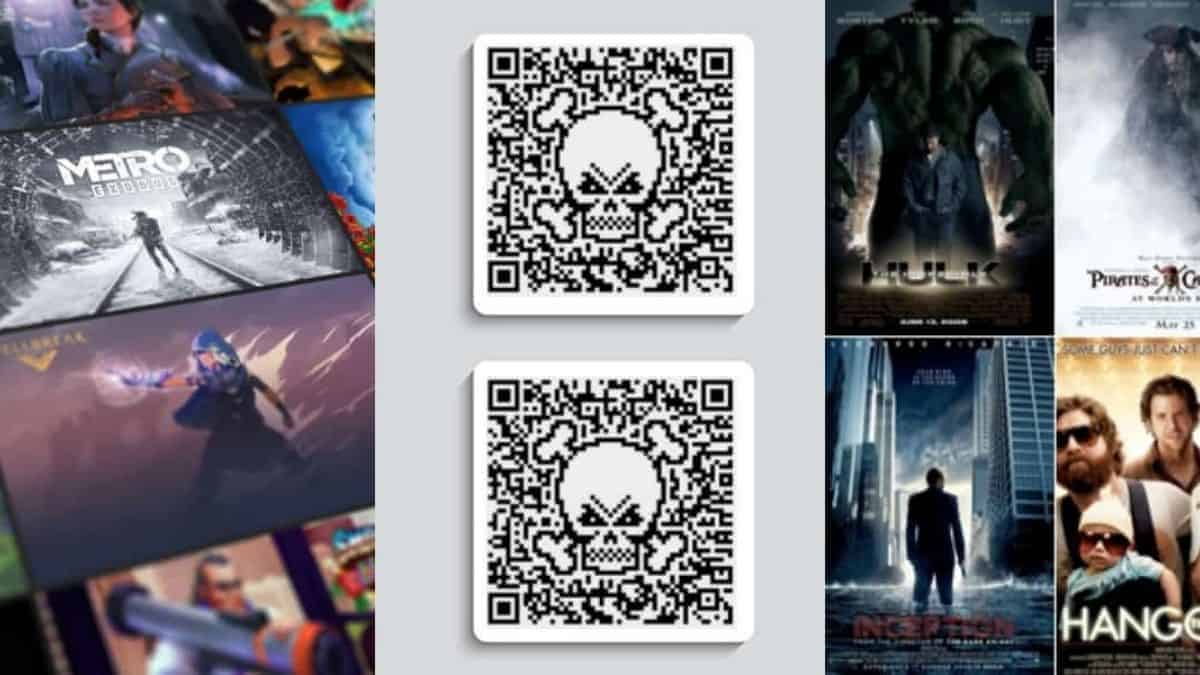
As per the sources, ChromeLoader is a Chrome browser plugin that is delivered as ISO files via pay-per-install websites and phishing social media postings that promise QR codes, pirated movies, and cracked video games. ChromeLoader changes web browser settings to display search results that lure users to download unwanted software, visit dating sites or adult games platforms, and participate in fake surveys. It stands apart among other browser hijackers for its incredible persistence, infection route, and volume involving abuse of PowerShell.
According to the sources, we came to know about the process of the malware attack and this is how it works. To infiltrate the system, the malware operators employ a malicious ISO archive file. This file is advertised as a cracked executable for commercial software or a video game, allowing victims to download it via malicious websites or torrents. Malware authors also market the harmful program through Twitter messages.
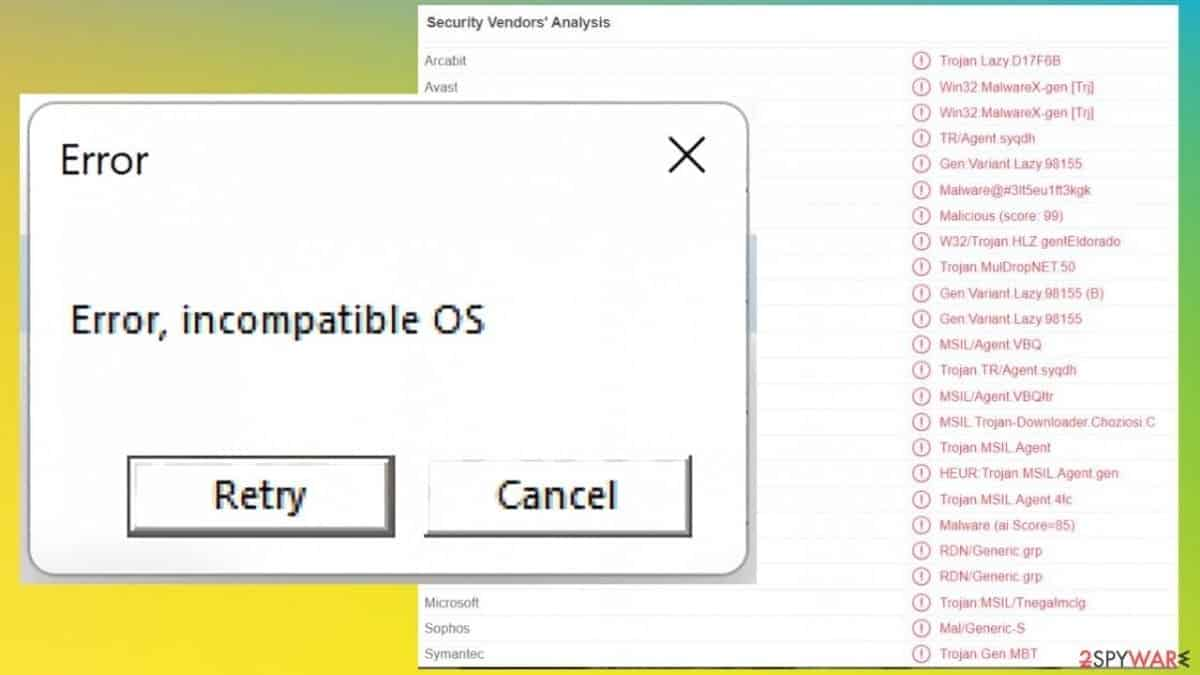
The file is mounted as a virtual CD-ROM drive when a user double-clicks it in Windows 10 or later systems. The software in this ISO file, CS Installer.exe, appears to be a keygen or game crack, but it unleashes the infection. ChromeLoader then runs/decodes a PowerShell command to retrieve an archive from the remote resource and installs it as a Chrome extension on the system. Following that, PowerShell deletes the scheduled task and infects Chrome with a hidden plugin that hijacks and manipulates the browser’s results. As per the Red Canary researchers, they stated that The ChromeLoader exploits macOS computers to manipulate the Safari and Chrome web browsers. On macOS, the infection chain is identical, but instead of ISO files, attackers utilize DMG (Apple Disk Image) files.
Moreover, with macOS, an installer bash script is used to download and extract the malware extension onto the private/var/tmp directory, rather than the executable containing the installer.


