The SolarWinds business at the heart of the Orion hack is scrutinized

SolarWinds, the Texas-based firm whose tech was hacked when serving some of the biggest institutions and corporations in the United States, was demonstrated by the announcement that elite cyber agents have carried out the largest attack against US officials in years in recent months.
SolarWinds provides businesses and government departments around the world with computer networking monitoring services and has been a major player since it was founded in 1999.

Rob Oliver, a research analyst at Baird who has followed the company for years said that They’re not the same kind of household name as Microsoft. That is because, in the backroom, their tech sits. He added: “Workers could have spent their whole career without hearing about SolarWinds. But I guarantee your IT department will know about it.”
The company was founded in Tulsa, Oklahoma by two brothers, ahead of the feared turn-of-the-millennium Y2K computer bug. On an earnings call in October, Kevin Thompson, chief executive of the group, touted how far it has since come.
There was no database or IT implementation model out there for which, he told analysts, the organization did not have any form of control or management. “We don’t think anyone else in the market is even close in terms of the breadth of coverage we have,” he said.
However, supremacy has become a liability. SolarWinds warned thousands of its customers on Sunday that an “outside nation-state” had discovered a back door in its most famous device, an instrument called Orion that lets companies track outages on their computer networks and servers.
The organization announced that hackers snuck a malicious code into an Orion upgrade that allowed them remote access to the networks of customers. SolarWinds acknowledged that the hack started as early as March, allowing the hackers plenty of time to enter the internal workings of the clients.
The breach was not found until the popular cybersecurity firm FireEye, which uses SolarWinds itself, decided that through the software it had suffered a breach. FireEye did not officially accuse the SolarWinds hack of the leak, but it allegedly stated that it was the case on Tuesday at the tech site Krebs On Defense.
FireEye identified the dizzying capabilities of the malware, from initially lying inert until two weeks, to hiding in plain sight by masking its reconnaissance forays as an operation of Orion.
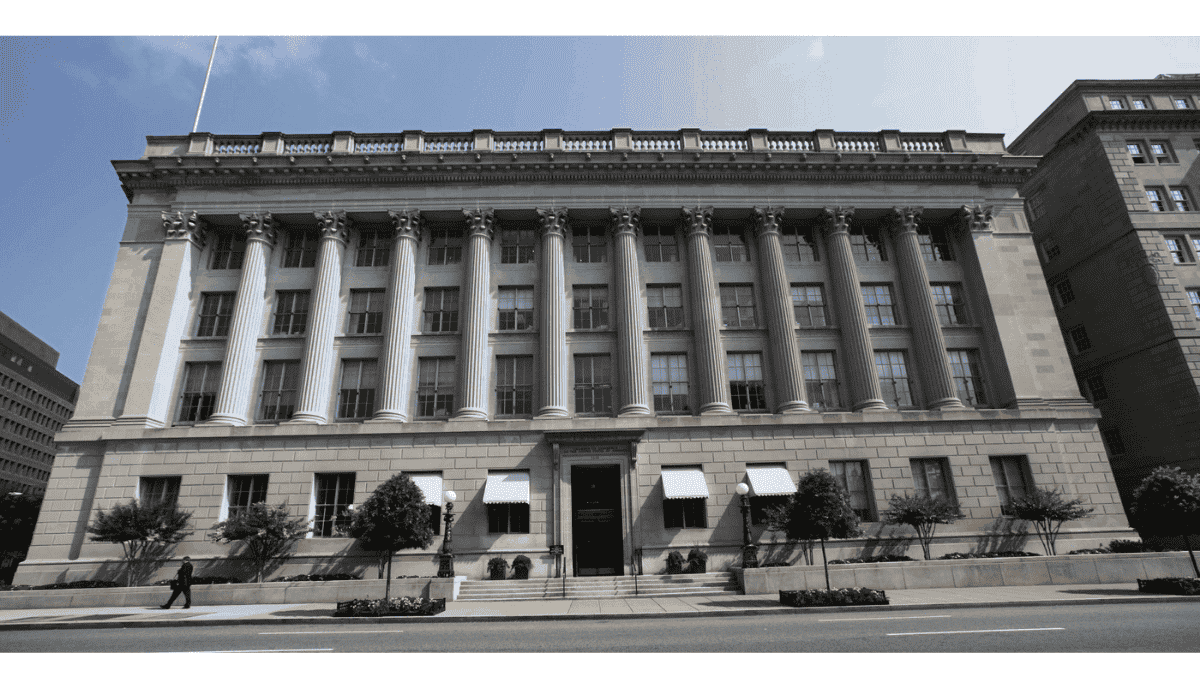
It is not yet clear about the effect of the hack. US government officials have not yet confirmed which departments were affected. But the departments of treasury and commerce were confirmed to have been hit.
The FBI, the Cybersecurity and Infrastructure Security Agency, and the Director of National Intelligence’s office described the breach as “significant and ongoing” in a joint statement released Thursday evening.
“This is a developing situation, and while we continue to work to understand the full extent of this campaign, we know this compromise has affected networks within the federal government,” the statement read.
In a financial statement, SolarWinds estimated that about 18,000 customers had installed the corrupted app, indicating that at any point this year all of them were vulnerable to spy operations.
Earlier this week the corporation downloaded a web page of hundreds of its best-known clients, from the White House, the Pentagon, and the Secret Service to the McDonald’s restaurant chain and museums in Smithson.
Kim Peretti, who co-chairs Atlanta-based law firm Alston & Bird’s cybersecurity preparedness and response team said that for several months, if not more, if not ever, they will not know the true effect.
FireEye has announced that it has confirmed infections in North America, Europe, Asia, and the Middle East, including in the health care and oil and gas sectors, without specifying any particular targets, and has notified affected customers around the world.
The violation has led SolarWinds to undergo a crisis. The tainted commodity accounted for almost half of the annual sales of the firm, which totaled $753.9 million over this year’s first nine months. Since the beginning of the week, the portfolio has fallen 23 percent.
On Wednesday, Moody’s Investors Service said it was looking to downgrade its rating for the company, citing the “potential for reputational damage, a material loss of customers, business performance slowdown and high remediation and legal costs.”
The longtime CEO of SolarWinds, Kevin Thompson, had suggested months earlier that he would quit at the end of the year while the firm considered selling off one of its subsidiaries. Just a day before FireEye first officially announced the hack, the SolarWinds board named his successor.
Executives of SolarWinds denied interviews via a spokeswoman, who cited an open probe that now encompasses the FBI and other agencies.
In a statement issued to Reuters on Sunday, the company said “we strive to implement and maintain appropriate administrative, physical, and technical safeguards, security processes, procedures, and standards designed to protect our customers.”

