Should you disable xmlrpc.php in WordPress?

WordPress has always had in-built functions that permit you remotely interact along side your site. face it, from time to time you’ll got to access your web site and your laptop won’t be anywhere nearby. for an extended term, the answer become a report named xmlrpc.personal home page. however in latest years, the report has find yourself more of a pest than an answer .
Below we dive into what XML-RPC. Hypertext Preprocessor really is and why it becomes created. we additionally evaluate the commonplace protection troubles its reasons and how to patch them on your own WordPress website.
What’s xmlrpc.php?
XML-RPC may be a function of WordPress that permits information to be transmitted, with HTTP performing because of the transport mechanism and XML because of the encoding mechanism. as long as WordPress isn’t a self-enclosed machine and once in a while desires to speak with other structures, this became sought to deal with that process.
As an instance, allow’s say you wanted to undergo your site from your cell tool because your laptop become nowhere accessible . you’ll use the faraway get admission to function enabled through xmlrpc.phpTo do exactly that.
The middle capabilities that xmlrpc.php enabled were allowing you to attach to your website online via cellphone, enforcing trackbacks and pingbacks from other internet sites , and a couple of capabilities associated with the jetpack plugin.
Why become xmlrpc.php created and therefore the way become it used?
The implementation of XML-RPC goes again to the first days of WordPress before it even became WordPress.
Returned within the youth of the web, when the connections had been particularly slow, the system of writing and publishing to internet become plenty harder and time-ingesting. rather than writing within the browser itself, the bulk would write offline, then copied and pasted their content material onto the online. still, this system becomes away from best.
The solution (at the time), become to make an offline running a blog purchaser, where you’ll compose your content, then connect together with your blog to publish it. this connection was administered through XML-RPC. with the first framework of XML-RPC in location, early apps used this identical connection to allow people to log in to their WordPress sites from different devices.
XML-RPC Nowadays
In 2008, with version 2.6 of WordPress, there was a choice to enable or disable XML-RPC. However, with the discharge of the WordPress iPhone app, XML-RPC support was enabled by default, and there was no choice to close up the setting. This has remained faithful to this day.
However, the functionality of this file has greatly decreased over time, and therefore the overall size of the file has decreased from 83kb to 3kb, so it doesn’t play as large of a task because it wont to .
The Future of XML-RPC
With the new WordPress API, we will expect XML-RPC to be eliminated entirely. Today, this new API remains within the trial phase and may only be enabled through the utilization of a plugin.
However, you’ll expect the API to be coded directly into the WordPress core within the future, which can mostly eliminate the necessity for the xmlrpc.php file altogether.
The new API isn’t perfect, but it provides a more robust and secure solution to the matter that xmlrpc.php addressed.
Why you ought to Disable Xmlrpc.php
The biggest issues with XML-RPC are the safety concerns that arise. the problems aren’t with XML-RPC directly, but instead how the file is often wont to enable a brute force attack on your site.
Sure, you’ll protect yourself with incredibly strong passwords, and WordPress security plugins. But, the simplest mode of protection is to easily disable it.
There are two main weaknesses to XML-RPC which are exploited within the past.
The first is using brute force attacks to realize entry to your site. An attacker will attempt to access your site using xmlrpc.php by using various username and password combinations. they will effectively use one command to check many different passwords. this enables them to bypass security tools that typically detect and block brute force attacks.
The second was taking sites offline through a DDoS attack. Hackers would use the pingback feature in WordPress to send pingbacks to thousands of web sites instantaneously. This feature in xmlrpc.php gives hackers an almost endless supply of IP addresses to distribute a DDoS attack over.
To check if XML-RPC is running on your site, then you’ll run it through a tool called XML-RPC Validator. Run your site through the tool, and if you get a mistake message, then it means you don’t have XML-RPC enabled.
If you get a hit message, then you’ll stop xmlrpc.php with one of the 2 approaches below.
Method 1: Disabling Xmlrpc.php With Plugins
Disabling XML-RPC on your WordPress site couldn’t be easier.
Simply navigate to the Plugins › Add New section from within your WordPress dashboard. look for Disable XML-RPC and install the plugin that appears just like the image below:
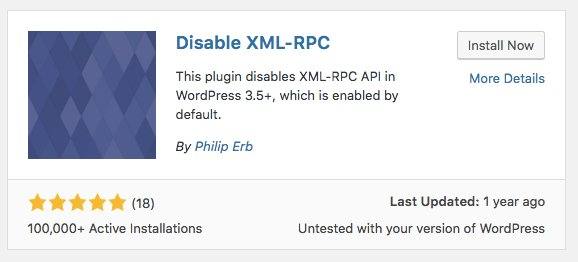
install disable xmlrpc plugin
Activate the plugin and you’re ready . This plugin will automatically insert the required code to show off XML-RPC.
However, confine mind that some existing plugins may utilize parts of XML-RPC, so disabling it completely could cause a plugin conflict or certain elements of your site to not function.
If you’d want to only turn certain elements of XML-RPC off, but still allow certain plugins and features to figure , then use the subsequent plugins instead:
Stop XML-RPC Attack. This plugin will stop all XML-RPC attacks, but it’ll still allow plugins like Jetpack, and other automatic tools and plugins to retain access to the xmlrpc.php file.
Control XML-RPC Publishing. this enables you to retain control and use over the remote publishing option afforded by xmlrpc.php.
Method 2: Disabling Xmlrpc.php Manually
If you don’t want to utilize a plugin and like to try to to it manually, then follow this approach. it’ll stop all incoming xmlrpc.php requests before it gets passed onto WordPress.
Open up your .htaccess file. you’ll need to activate the ‘show hidden files’ within file manager or your FTP client to locate this file.
Inside your .htaccess file, paste the subsequent code:
- # Block WordPress xmlrpc.php requests
- <Files xmlrpc.php>
- order deny,allow
- deny from all
- allow from xxx.xxx.xxx.xxx
- </Files>
Note: Change xxx.xxx.xxx.xxx to IP address you would like to permit access xmlrpc.php or remove this line completely.
Closing Thoughts
Overall, XML-RPC was a primary solid solution to a number of the issues that occurred thanks to remote publishing to your WordPress site. However, with this feature came some security holes that ended up being pretty damaging for a few WordPress site owners.
To ensure your site remains secure it’s an honest idea to disable xmlrpc.php entirely. Unless you need a number of the functions needed for remote publishing and therefore the Jetpack plugin. Then, you ought to use the workaround plugins that leave these features, while still patching the safety holes.
In time, we will expect the features of XML-RPC to become integrated into the new WordPress API, which can keep remote access and therefore the like, without sacrificing security. But, within the meantime, it’s an honest idea to guard yourself from the potential XML-RPC security holes.
Have you blocked XML-RPC access via a plugin or manually? Or experienced any security issues from having it active within the first place? Please share your experience within the comments below.


